Safeguarding CNC Machines in Networked IT/OT Environments

Report by Danny Weller
Navigating the intersection of Informational Technology (IT) and Operational Technology (OT) environments can be a tricky business. Safeguarding CNC machines in this space is an essential process. Striking a balance between advancing intelligence and efficiency while mitigating the risks of exposing OT systems to the broader digital landscape is crucial. Explore the intricacies with our insightful guide.
IT/OT networking stands as a pivotal element in the realm of Industry 4.0, interlinking technologies across industrial enterprises to facilitate centralized control and enhanced access to information. The pursuit of these advantages holds the potential to nearly double the scale of the industrial automation and software market, projecting an increase from the current $200 billion to an estimated $400 billion by 2028.
However, integrating traditionally isolated OT (operational technology) networks with more open IT environments introduces risks that many OT systems were not originally designed to confront. The nature and origin of these risks vary depending on the type of OT in question. Here we will focus on the challenges presented by this integration to one such technology: computer numerical control (CNC) machines.
CNC Technology
CNC machines are used in reductive manufacturing processes, anything that requires drilling, routing, lathing, or other removal of raw material. Their computer-controlled functions make them extraordinarily precise, capable of working within finer parameters than humans can perceive with their natural senses—to about 10 microns. Because CNC machines have not historically had—or needed—built-in security features, networking them with enterprise IT devices brings a range of cybersecurity risks.

Image: Getty Images
Why do CNC Machines Need Protection?
CNC machines come with a substantial price tag, often reaching tens of thousands of dollars, and their components are costly to replace if they wear out or break. These machines are utilized in diverse applications, crafting products ranging from airplane parts to hip replacement prosthetics, emphasizing the paramount importance of quality and reliability. Any malicious tampering by a bad actor can result in severe consequences, whether financial implications or risks to human health and safety.
Within every CNC machine lies an interior processing area dedicated to machining. Its intricate system includes multiple moving parts, such as an automated dolly for raw material positioning and a spindle that rotates at varying speeds for drilling, routing, lathing, and other actions. The computer-controlled system not only orchestrates these actions but also receives sensor inputs to monitor factors like waste buildup, heat thresholds, positioning errors, and more.
Despite their advanced mechanical and computational capabilities, CNC machines operate on surprisingly simple software, primarily relying on legacy Linux or Windows operating systems and code written in relatively basic programming languages. The command line interface allows anyone with access to input commands for execution. While these pose minor risks in closed environments with trusted personnel, the stakes rise significantly when a CNC machine is exposed to the external world. In a networked IT/OT environment, threats can infiltrate CNC machines even without direct access from an attacker. IT users engaging with vulnerable websites or falling victim to phishing emails can introduce threats into the corporate network, ultimately spreading to the OT side and affecting individual machines.
The supply chain presents another avenue of risk due to the diverse range of participants involved, including numerical controller manufacturers, machine builders, retailers, and integrators. This complexity in the supply chain creates numerous opportunities for threats to be injected. Given that CNC machines are often highly customized, the extensive involvement of various entities throughout the process from manufacturing to installation and configuration introduces multiple points of vulnerability.

Image: Getty Images
What Are the Risks?
The use of legacy software and basic code in CNC machines renders them vulnerable to exploitation by attackers. When integrated into an IT/OT network, these machines may inadvertently disclose information like product counts and machining instructions through their interfaces. In numerous settings, authentication measures and access controls for CNC machines are often disabled, as they were historically considered unnecessary, allowing virtually anyone to interact with the controller without proper safeguards. Collectively, these vulnerabilities make networked CNC machines prone to remote code execution and other malicious manipulations.
The utilization of remote code poses the risk of exfiltrating sensitive data, including intellectually valuable competitive information. Malicious commands can have severe consequences, such as disabling crucial safety features or manipulating parameters to degrade performance or harm the machine. For instance, every CNC machine is equipped with a "feed hold" function, which stops all moving parts to allow operators to access the process area for cleaning and other tasks. If this function is disabled, it poses a significant risk to the operator's safety. Similarly, altering the machine's thresholds for tool load or part wear can lead to breakdowns from overuse or prompt unnecessary replacements, resulting in financial harm and potentially creating health and safety hazards.

Image: Getty Images
How to Protect CNC Machines
To safeguard CNC machines in networked IT/OT environments, several immediate steps can be implemented. Firstly, conducting a comprehensive inventory of all CNC tools is essential to maintain a clear and up-to-date understanding of the network's composition. Segregating the CNC machine network into its own segment is advisable, allowing for more straightforward monitoring of traffic flows, with the ability to cut off access if necessary. Additionally, deploying intrusion prevention systems (IPS) and firewalls adds an extra layer of protection to enhance overall security.
To minimize risk, it's crucial to patch any patchable legacy software associated with CNC machines. While direct interference with the CNC machine may be restricted to avoid impacting its warranty, deploying additional security measures around the machine can still enhance protection in such cases. Furthermore, enabling access and authentication controls is imperative. Default passwords, such as "admin," should be promptly replaced with robust, customized alternatives. This practice is essential for both on-site access and remote connections into the OT environment and CNC machines, ensuring a higher level of security.
Three Step Approach
In a broader context, a comprehensive three-pronged defense strategy is recommended for networked IT/OT environments:
- Specialized Mitigation Measures:
Deploy targeted mitigation measures designed specifically for OT assets and networks, as outlined earlier for CNC machines.
- Attack Surface Risk Management:
Embrace an attack surface risk management approach to thoroughly understand the entire IT/OT attack surface. This involves assessing associated assets, identifying their respective risk levels, and implementing appropriate risk mitigation strategies.
- Context-Aware Detection and Response:
Implement context-aware detection and response capabilities, such as Extended Detection and Response (XDR). These systems can effectively detect cyber incidents, provide insights to swiftly isolate the root cause, and facilitate the implementation of the necessary response measures.

Image: Ondrej Neduchal
Navigating the Future: Securing IT/OT Networks and Tools
As IT/OT networking emerges as the future standard, safeguarding the distinct vulnerabilities of tools like CNC machines becomes pivotal for shielding businesses against potential threats to data, safety, and financial integrity. Tailoring mitigation measures to the unique technology and organizational landscape is essential. Moreover, fortifying networked IT/OT environments involves the adoption of attack surface risk management approaches. By deploying context-aware detection and response capabilities, businesses can establish a proactive and robust security posture, ensuring comprehensive defense against evolving challenges.
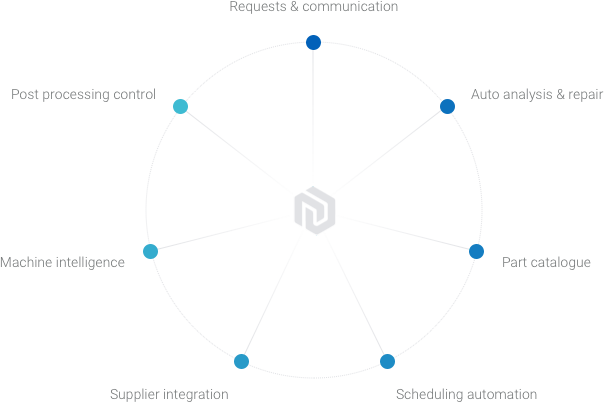
About AMFG
We work with hundreds of machine shops to enhance and accelerate their quoting process. Take control of your quoting procedure and streamline your pre-production workflow: our real-time inventory management empowers you to efficiently oversee your resources, leading to a smoother and more productive operation. Whether you’re an SME machine shop or a multinational OEM, AMFG offers a comprehensive end-to-end MRP system to enhance your inquiries, quoting, and pre-production processes. Find out how AMFG can supercharge your CNC Machining processes today.

.svg)
.svg)






.avif)

.svg)